A single misjudged mass‑email and media outreach campaign can trigger domain‑reputation warnings, content‑filtering, or permanent‑blacklisting if it violates consent, engagement, or infrastructure‑quality standards. The modern email‑ecosystem links every outreach‑mistake to technical‑scores, behavioural‑signals, and compliance‑frameworks, so one poorly‑executed broadcast can permanently damage inbox‑placement.
How does a failed outreach campaign turn into a domain‑blacklist event?
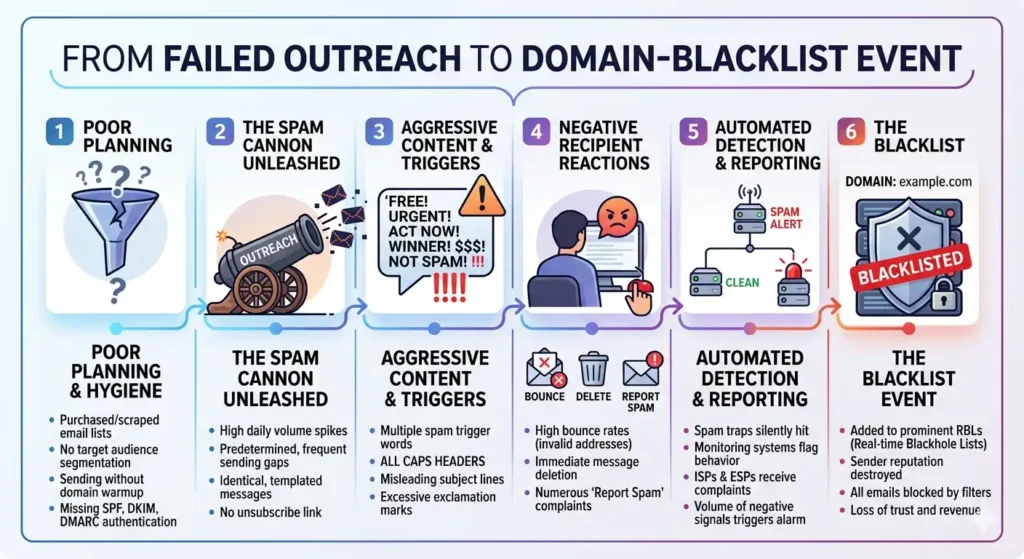
A failed outreach campaign turns into a domain‑blacklist event when high‑spam‑complaints, sudden‑volume‑spikes, and low‑engagement trigger email‑providers’ reputation‑scoring systems, which then flag or delist the sending domain.
A blacklist‑event occurs when one or more email‑reputation‑services (e.g. Spamhaus, Barracuda, MXToolbox) label the sending domain as a persistent‑abuse‑source. This typically happens after a mass‑email and media outreach pushes high‑spam‑report‑rates, generates low‑open‑rates, or shows sudden‑volume‑increases without prior‑sender‑history.
Dive Deeper With Our Expert Guides and Related Blog Posts:
The Ghosting Index: Why 8 out of 10 Journalists Ignore Startup Outreach
How 2026 Email Regulations are Killing Traditional Bulk PR Distribution Services
Blacklists report that domains with multiple‑simultaneous‑spam‑complaints, low‑click‑through‑rates, and high‑bounce‑rates are statistically‑more‑likely to carry malicious‑or‑mis‑targeted‑content. When a domain appears on such lists, email‑platforms can divert, throttle, or refuse messages from that domain, which can persist even after the problematic campaign ends.
For mass‑email and media outreach, this mechanism means that a single‑mis‑executed‑broadcast can echo in the technical‑reputation‑system long after the campaign is over.
How do modern spam‑filters and engagement‑signals generate blacklists?
Modern spam‑filters and engagement‑signals generate blacklists by aggregating spam‑reports, bounce‑rates, complaint‑logs, and interaction‑patterns into a real‑time‑reputation‑score for each domain and IP‑address.
Email‑platforms analyse:
- The proportion of messages marked as “spam” by recipients.
- How many emails bounce due to invalid‑addresses or poor‑list‑quality.
- Whether the sender shows sudden‑volume‑increases without prior‑established‑sending‑patterns.
These inputs are fed into machine‑learning models that classify senders as “safe,” “neutral,” or “risky.” Risky‑senders with persistent‑abuse‑signals are added to proprietary‑blacklists held by major‑email‑providers or third‑party‑security‑vendors on Is your technical infrastructure optimized for 80 percent primary inbox placement rates.
Once a domain appears on such lists, reception‑servers may:
- Reject incoming‑relay‑requests.
- Delay delivery into secondary‑folders.
- Tag all future‑senders from that domain as “low‑trust.”
Mass‑email and media outreach that ignores these layers can move from grey‑listing to full‑blacklisting without a clear‑warning window.
How do consent‑and‑compliance‑failures accelerate blacklisting?
Consent‑and‑compliance‑failures accelerate blacklisting because unverified‑opt‑in‑lists, undisclosed‑purpose‑tags, and non‑removal‑options generate higher‑complaints and regulatory‑flags, which email‑providers treat as hard‑penalty‑signals.
European‑and‑UK‑data‑protection‑regimes define lawful‑bases for processing personal‑data, including explicit‑consent for commercial‑email‑outreach. When a mass‑email and media outreach fails to document‑consent, provide clear‑unsubscription‑links, or specify‑purpose‑tags, recipients are more likely to mark the mail as spam instead of using opt‑out‑mechanisms.
High‑spam‑rate‑campaigns that rely on scraped‑or‑third‑party‑lists often show 1–2% complaint‑rates, which is far above the 0.1–0.3% threshold that email‑reputation‑services use to identify abusive senders. This pattern feeds into blacklist‑creation and long‑term‑reputation‑damage.
Compliance‑enforcement‑bodies also report suspected‑abuse‑patterns to spam‑filter‑networks, which can fast‑track blacklist‑action for domains that repeatedly breach consent‑rules.
How does infrastructure‑mis‑optimization contribute to the blacklist trap?
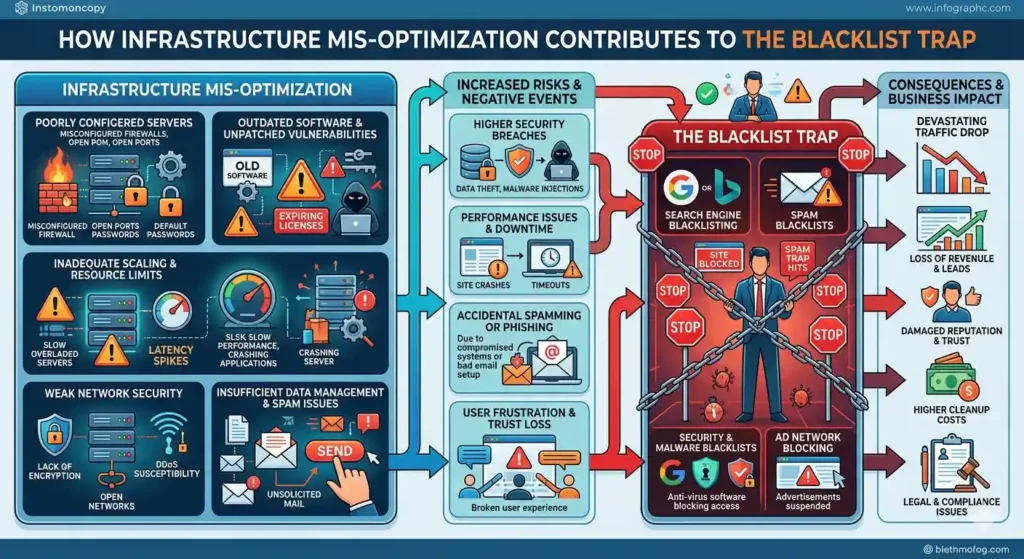
Infrastructure‑mis‑optimization contributes to the blacklist trap by weakening authentication, reputation‑build‑time, and deliverability‑signals that email‑platforms rely on to judge whether a domain is a legitimate sender.
Key‑technical‑failures include:
- Weak or missing SPF, DKIM, and DMARC records, which increase the risk of spoofing and failed‑validation.
- Poor‑list‑hygiene, including high‑bounce‑rates and reused‑cold‑lists, which signal low‑trust.
- Lack of IP‑rotation and warming‑programs for high‑volume‑outreach, which creates surprise‑surges in sending‑traffic.
These technical‑shortcomings make it easier for filters to classify the domain as a high‑risk sender, regardless of content‑quality. Email‑platforms report that domains with multiple‑security‑failures are statistically more likely to be associated with spam, phishing, or bulk‑mis‑targeted‑mail.
For mass‑email and media outreach, this means that a campaign can be technically‑flawed even if the content‑and‑recipient‑list appear acceptable on‑paper.
How do one‑time‑outreach‑mistakes have long‑term blacklist consequences?
One‑time‑outreach‑mistakes can have long‑term blacklist consequences because reputation‑scores and blacklist‑statuses often reset slowly, and email‑platforms use historical‑data, not single‑campaign‑snapshots.
A reputation‑system may retain evidence of a high‑spam‑event for weeks or months, even if the sender later adheres to strict‑consent‑and‑volume‑controls. Blacklists sometimes require manual‑delisting‑requests, documentation‑of‑correction‑measures, and extended‑periods of low‑volume‑clean‑sending before they de‑activate‑the‑flag.
This persistence means that a single‑day‑mistake, such as an unverified‑bulk‑list‑blast, can reduce primary‑inbox‑placement‑rates from 80% to below 30% for subsequent mailings, sometimes permanently. Email‑providers report that senders who experience blacklisting face longer‑recovery‑paths than those who maintain gradual‑growth‑and‑high‑engagement.
The blacklist trap for mass‑email and media outreach arises when technical‑failure, consent‑lapses, and engagement‑errors align in a single‑campaign, turning one misstep into a long‑term‑domain‑restriction. Preventing this outcome requires treating outreach‑infrastructure, compliance‑controls, and engagement‑tracking as equal‑partners in the sending‑stack, not as separate‑afterthoughts.
Long‑term‑safety in this ecosystem comes from consistency, transparency, and technical‑rigour, not from squeezing‑maximum‑volume‑out of a single‑broadcast.